When it comes to the best way to store your crypto seed phrase, simplicity is king. You need an offline backup of your 12- or 24-word phrase, completely isolated from physical and digital threats.
This means you’re going to write it down on paper or, even better, engrave it onto metal. That physical copy then goes into a secure, private location. This old-school, non-digital approach isn't just a suggestion—it's the gold standard for protecting your crypto.
Why Securing Your Seed Phrase Is Everything
Get this straight: your seed phrase is the absolute master key to your funds. It’s not just another password. It’s the very source code from which all your wallet's private keys are born.
For a merchant, this phrase is the title deed to your business property and the combination to the vault, all rolled into one. If you lose it, your funds are gone. Forever. If it gets stolen, same story.
There’s no "Forgot Password" link or customer support hotline to call in the world of self-custody. You are the bank. While that level of control is empowering, it comes with the non-negotiable job of protecting that master key. Getting your seed phrase storage right isn't a minor detail; it's the bedrock of your entire operational security. And to really grasp its weight, it helps to understand the wider world of cryptocurrency.
Seed Phrase Storage Methods At a Glance
So, how should you store it? Choosing the right method is a balancing act between security, durability, and what makes sense for your business. A text file on your computer is convenient but an absolute security nightmare. A metal plate locked in a safe is rock-solid but obviously not something you can access in a hurry.
Let’s quickly break down the most common options people consider.
| Storage Method | Security Level | Durability | Primary Risk |
|---|---|---|---|
| Paper Backup | High (if offline) | Low | Physical damage (fire, water, fading) |
| Metal Backup | Very High | Very High | Physical theft or loss |
| Digital File (Unencrypted) | Very Low | High | Hacking, malware, device failure |
| Password Manager | Low | High | Online attacks, platform breaches |
The takeaway here is pretty clear: offline, physical backups are in a league of their own. Your number one goal is to sever any and all connections to the internet, because that’s where nearly all theft happens.
The Brutal Reality of a Compromised Seed Phrase
Let's paint a picture. An employee clicks a bad link and accidentally downloads malware that starts sniffing around your company’s cloud drive. If a digital copy of your seed phrase is sitting in a text file there, a hacker can drain your entire business wallet in minutes. No second chances, no way to get it back.
This isn’t a scare tactic; it’s a scenario that plays out far too often.
A compromised seed phrase gives an attacker complete and irreversible control of your funds. They don't need your PINs, passwords, or 2FA codes. They just restore your wallet on their own device and send everything to themselves.
This guide will walk you through the practical, business-ready steps for generating, backing up, and protecting your seed phrase. We'll cover everything from air-gapped computers to multisig protocols, making sure your assets stay exactly where they belong: with you.
Generate Your Seed Phrase in an Air-Gapped Setup
The single most important moment in your wallet's life is its creation. How you generate your seed phrase sets the security standard for everything that follows. The gold standard here is creating it in a completely offline, or air-gapped, environment.
An air-gapped setup means the device generating your keys has never touched the internet and never will. Think of it as a digital cleanroom. This simple act prevents your master key from ever being exposed to malware, keyloggers, or any online snoops. For any serious merchant, this isn't just a recommendation—it's step zero.

Selecting and Verifying Your Hardware
Your choice of hardware is everything. You'll want a device built from the ground up with security and Bitcoin-only principles in mind. A great example is the Coldcard, which has earned a solid reputation for its robust, air-gapped capabilities. These aren't just wallets; they're purpose-built security devices designed to generate and store keys without ever needing a direct line to an online computer.
Before you even plug it in, you need to play detective.
- Inspect the packaging: Reputable manufacturers use tamper-evident seals or bags. If a seal is broken, peeling, or just looks off, stop right there. Don't use it.
- Check the device itself: Look for any signs it’s been opened. Scratches around the seams, weird glue residue, or parts that don't quite line up are all red flags. A compromised device is a game-over scenario.
- Run the manufacturer's check: During setup, many of the best hardware wallets have a step to verify the device's firmware against the official signature from the factory. Never skip this.
Here’s a classic mistake I see merchants make: buying hardware from a third-party reseller on Amazon to save $20. Always, always buy directly from the manufacturer. It’s the only way to be sure you aren’t getting a cleverly disguised counterfeit.
The Generation Process
With your verified device in hand, it's time to generate the phrase. The environment matters more than you think. Don't do this in a coffee shop, your open-plan office, or anywhere with security cameras. A private room at home or the office after hours is what you're looking for.
The process itself is simple. You’ll power on the device—ideally with a battery or a power-only USB connection to a wall outlet, not your computer—and start the "new wallet" setup. The device’s secure hardware will then generate a 12 or 24-word seed phrase.
This is it. The most sensitive moment of your wallet's existence.
The seed phrase is displayed on the device's screen just one time. There is no "forgot my password" option. You have to get this right, right now.
Recording Without a Digital Footprint
The "no digital footprint" rule is absolute. I cannot stress this enough. You cannot, under any circumstances, use a digital tool to record your seed phrase.
- No photos. Don't even think about taking a picture with your phone.
- No text files. Don't type it into a notes app, a Word doc, or an email draft, not even for a split second.
- No printers. A network printer is just another computer that can be compromised.
Go old school: pen and paper.
Write each word down clearly. Double-check the spelling. Number them 1 through 12 or 1 through 24. A simple mistake, like swapping word #8 and #9, renders the entire backup useless. After you've written it down, the hardware wallet will usually quiz you, asking you to confirm a few of the words. This final check is your last chance to ensure the paper backup you’re holding is a perfect match.
Choose the Right Physical Backup Medium
So you've generated your seed phrase and written it down. Congratulations, you're now holding the literal keys to your business's Bitcoin. But let's be honest—that piece of paper is flimsy. It’s one spilled coffee, one leaky pipe, or one office fire away from becoming worthless ash.
Effective crypto seed phrase storage isn't just about jotting down the words. It’s about engraving them into something that can survive the chaos of the real world.

This is where metal backups come into play. Paper is a fine starting point, but it should only ever be temporary. For serious, long-term security, especially for a business, you need a medium that can take a beating. When you're thinking about this, it helps to frame it within the broader context of choosing the right backup systems for any critical data.
The move toward hardcore physical backups isn't just a niche idea; it’s a reflection of a booming market. In 2024, the global cold storage wallet market—which is completely reliant on secure seed phrases—was valued at $3.5 billion. Analysts expect it to explode to $12.2 billion by 2033, climbing at a 15.2% CAGR. That kind of growth tells you just how critical this piece of the puzzle is becoming.
Paper vs. Metal: A Durability Showdown
Picture this: faulty wiring sparks a small fire in your back office. Your paper backup, even if it’s tucked inside a "fire-resistant" bag, is probably toast. It'll be ruined by the heat, the smoke, or the water from the sprinklers.
A steel or titanium backup? It would emerge from the rubble completely unfazed, your seed phrase perfectly intact.
Let's break down the options:
- Paper: It’s cheap and easy, but it's also a liability. It tears, it fades, and it’s completely defenseless against fire and water. Use it to get the phrase from your hardware wallet to your metal backup, and that's it.
- Stainless Steel: This is a fantastic choice for most businesses. With a melting point around 2,500°F (1,370°C), it’ll survive any typical building fire. It also stands up well to corrosion and physical damage.
- Titanium: This is the top-tier option. Titanium's melting point is over 3,000°F (1,650°C), making it even tougher than steel. Its superior corrosion resistance makes it the go-to for anyone planning for extreme, multi-decade storage.
The rule of thumb is simple: your backup medium has to be tougher than its environment. For a business sitting on significant funds, a high-quality metal backup isn't an expense—it's essential insurance.
Comparing Metal Storage Solutions
Not all metal backups are the same. You’ll find several designs out there, each with a different way of recording your words. The two most popular styles are plates and capsules, with brands like Cryptosteel leading the charge.
Getting the small details right here is key to matching the solution to your operational security needs.
Stamped or Etched Plates
These are simple, flat plates of steel or titanium. You use a punch kit to stamp the words or a special tool to etch them directly into the metal.
- Pros: Extremely durable and easy to store discreetly—it just looks like a random piece of metal. The process is very straightforward.
- Cons: You'll need a separate stamping kit, and it can be loud and requires a bit of force. If you make a mistake, fixing it is a real pain.
Tile-Based Systems
These clever devices, like the ones from Cryptosteel, use a frame that lets you slide in pre-engraved letter tiles to spell out your seed phrase words.
- Pros: The process is clean, quiet, and forgiving. Make a mistake? Just slide the tile out and put the right one in. No hammering required.
- Cons: They tend to be a bit more expensive and are bulkier than a flat plate. You also have to be sure the device is securely locked, or the tiles could potentially fall out if it's dropped or opened.
Balancing Budget with Risk
For a solo creator or a small merchant, a basic $50 stamped steel plate is a massive security upgrade over a piece of paper. It immediately protects you from the most common disasters like fire and floods, all for a minimal cost.
But for a larger company managing a corporate treasury, the cost of a premium titanium solution is just a rounding error next to the assets it protects. In that scenario, spending $200 on a titanium capsule that can withstand almost anything is an obviously prudent decision.
Ultimately, your choice comes down to a simple risk assessment. What are the most likely physical threats to the location where you’ll store this backup? Pick the medium that shuts down those threats, period. Remember, the price of a robust metal backup is a one-time investment in the permanent security of your Bitcoin.
Use Multisig and Geographic Distribution
Relying on a single backup, even a tough metal one, is just asking for trouble. It creates a massive single point of failure. If that one backup gets lost, stolen, or destroyed in a fire, you’re right back where you started—with zero access to your funds. For any serious business operating with Bitcoin, that's just not an acceptable risk.
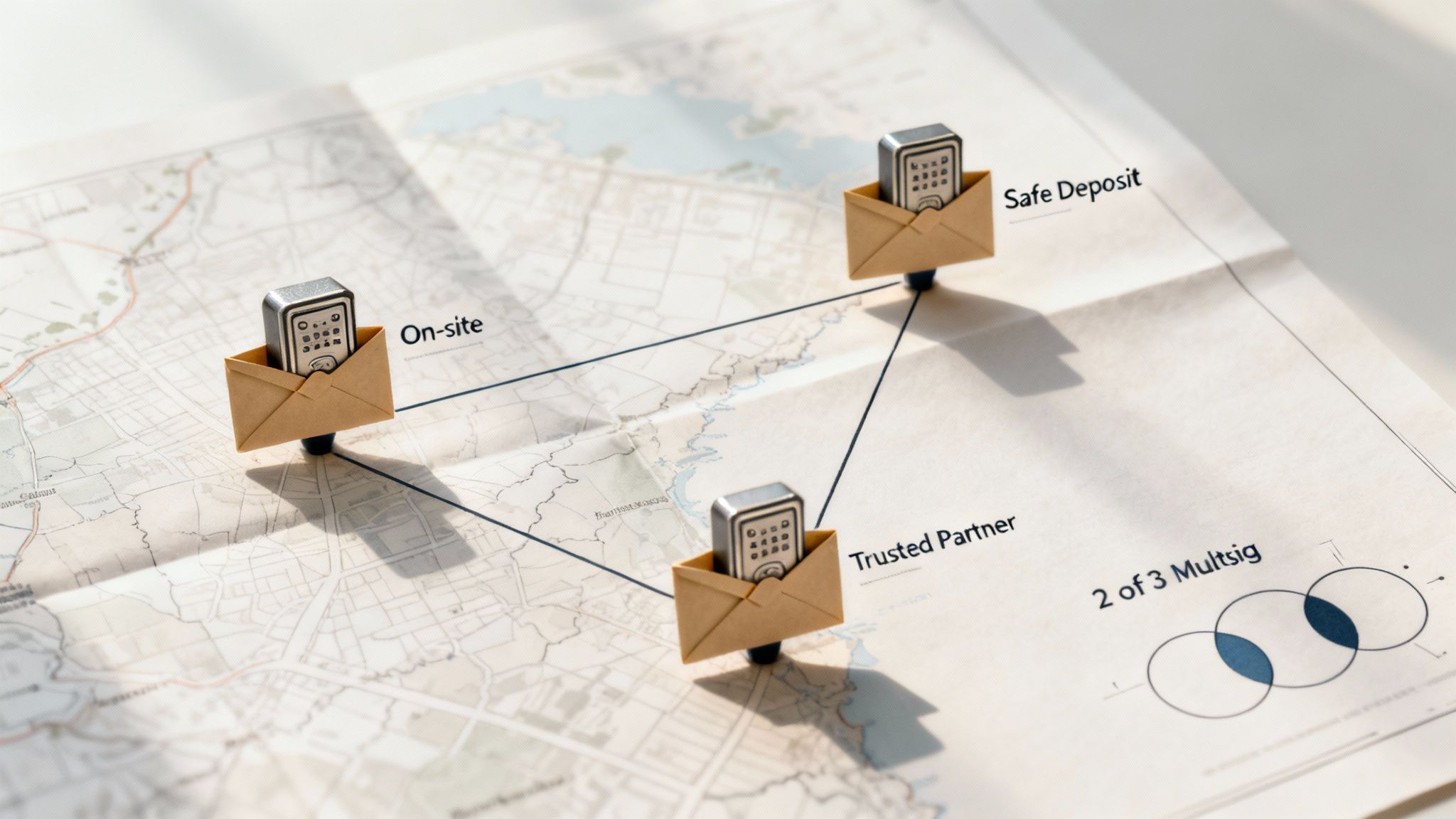
The real solution is to build redundancy and decentralization directly into your physical storage plan. This is where two powerful concepts come together: multisignature (multisig) wallets and geographic distribution. By combining them, you can build a system where no single person or disaster can compromise your funds.
What Is a Multisig Wallet?
Think of a standard Bitcoin wallet as a safe with a single key. A multisig wallet, on the other hand, is like a bank vault that needs multiple keys turned at the same time to open. Instead of one seed phrase controlling everything, a multisig setup gives you multiple, independent seed phrases (and their corresponding hardware wallets).
You can then decide how many keys are needed to sign a transaction. A 2-of-3 setup is a common and incredibly effective arrangement for a small business. This means you create three unique seed phrases and their backups, but you only need any two of them to access and move funds.
A 2-of-3 multisig setup makes the loss or theft of any single key a non-event. An attacker with one key has nothing, and an accident that destroys one key won't lock you out of your funds. It builds resilience right into your custody model.
Designing a Geographic Distribution Strategy
Once you have your multisig keys, the next step is to store them in completely separate and secure locations. The goal is to make it practically impossible for a single disaster—like a fire, flood, or targeted theft—to take out more than one key at a time. This is how you create a real-world security perimeter.
Here’s a practical scenario for a small Bitcoin business with two co-founders:
- Key 1 (On-Site): One hardware wallet and its metal seed backup are kept in a high-security safe at the main office. This gives you operational access when you need it.
- Key 2 (Off-Site Bank): The second hardware wallet and its metal backup go into a safe deposit box at a bank across town. It's secure, professionally monitored, and totally separate from your business premises.
- Key 3 (Trusted Third Party): The third set is entrusted to a secure third party, like a trusted family member or a business attorney, and stored at their location in another city or even another state.
This model protects against a whole range of threats. Fire at the office? The other two keys are safe. A co-founder's home is burglarized? The other keys are untouched. This strategy makes your security robust and multi-layered, moving beyond just protecting a single object to securing an entire system.
Unfortunately, far too many users still overlook the importance of offline, distributed storage. A comprehensive ACM study revealed a shocking statistic: 31% of surveyed cryptocurrency users chose to store their seed phrases with cloud services—a practice that flies in the face of all expert advice. It highlights a critical misunderstanding of how seed phrases, derived from standards like BIP39, grant total control over a wallet. You can read the full research about these security misconceptions to see just how common these mistakes are.
Best Practices for Splitting and Storing
Even if you aren't ready for a full multisig setup, you can still apply the principles of geographic distribution to a single seed phrase backup. But you have to be extremely careful here. Some people split their 24-word phrase into two or three pieces, storing each part in a different location.
While this might stop a casual thief, it introduces a ton of complexity and risk. If you lose just one of those pieces, the entire seed is gone for good.
A much better approach for a single-signature wallet is to create multiple, identical metal backups of the entire seed phrase and distribute those.
- Primary Backup: Stored in your main secure spot (e.g., a home or office safe).
- Secondary Backup: Stored at a separate, trusted location (e.g., a family member's house).
- Tertiary Backup: Stored in a bank safe deposit box.
This gives you redundancy against loss or destruction without the headache of splitting the phrase itself. Your crypto seed phrase storage is only as strong as its weakest link, and distributing identical copies is a straightforward way to eliminate that single point of failure.
Create a Recovery Plan and Access Protocol
Having a durable metal backup is a huge step forward, but honestly, it's only half the battle. A backup without a clear, documented recovery plan is just a piece of metal collecting dust. To do this right, you need a comprehensive protocol that anyone you trust can follow, even under immense pressure.
Think of it as the instruction manual for your vault. If you're ever unavailable or incapacitated, this document is the only thing standing between your business's Bitcoin and permanent loss. It has to be precise, unambiguous, and, most importantly, tested.
This kind of operational planning is more critical than ever. Attackers are getting smarter, shifting their focus to weak operational security. In fact, infrastructure attacks that compromise private keys and seed phrases dominated crypto thefts in 2025, leading to a staggering $2.2 billion in losses across 45 incidents.
That accounted for 76% of all theft that year, with the average breach hitting a devastating $48.5 million. This trend shines a spotlight on critical flaws in how businesses handle their seed storage protocols. You can dive deeper into these evolving threats to better understand how cold wallet security is changing.
Document Every Critical Detail
Your recovery plan should leave absolutely zero room for guesswork. It needs to contain every single piece of information a trusted party would need to successfully get your funds back online. And remember to store this document securely and separately from your seed phrase backups.
Here’s what your documentation must include:
- Exact Backup Locations: Don't just write "safe deposit box." Get specific. Note the bank branch, the box number, and list exactly who is authorized to access it. For backups kept at home, describe the location with pinpoint precision.
- Hardware Wallet Information: List the brand and model of the hardware wallet you used (e.g., Coldcard Mk4). This is crucial because recovery steps can vary slightly between devices.
- PIN Codes: Record the PIN for the hardware wallet. A PIN is useless if it's lost right when you need it most.
- BIP39 Passphrase Location: If you use a BIP39 passphrase (often called the "25th word"), never, ever store it with the 24-word seed. Your plan must state where this passphrase is, keeping it physically separate to maintain true two-factor security.
Draft a Succession Protocol
What happens if you're permanently unable to access the funds? A succession or inheritance protocol isn't optional for any serious business—it's a non-negotiable part of the plan. This designates who can take control and explicitly outlines the procedure for them to do so.
This is about more than just writing a name in a document. You need to make sure the designated individuals understand their role and have the necessary legal authority to act on your behalf.
Your succession protocol should be clear enough for a non-technical but trusted person to follow. This isn't just a technical guide; it's a continuity plan for your business's most critical asset.
Consider these elements when you're putting your protocol together:
- Identify Trusted Parties: Name the specific individuals (like a co-founder, a spouse, or a business attorney) who are authorized to kick off the recovery process.
- Define Triggering Events: Clearly state the conditions under which the protocol can be activated (e.g., death, medically confirmed incapacitation).
- Provide Contact Information: Include the contact details for legal counsel or technical experts who can assist the designated parties when the time comes.
Conduct Hands-On Recovery Drills
A plan you've never tested is just a theory. The only way to know for sure that your system works is to practice with it. Running a recovery drill—what we call a "fire drill"—builds confidence and exposes any weaknesses in your documentation or process before a real crisis hits.
The process itself is straightforward but absolutely invaluable. You'll simulate a total loss of your primary hardware wallet and try to restore access using only your backups and your documented recovery plan.
- Acquire a New Device: Get a new, unused hardware wallet of the same model.
- Follow Your Protocol: Hand the recovery document to a trusted partner or family member and have them follow the instructions exactly as you've written them. The key here is to resist the urge to help them. Let them struggle if they need to.
- Restore the Wallet: They should be able to locate the backups, enter the seed phrase into the new device, and successfully access a small test wallet you've set up for this purpose.
- Identify Gaps: Did they get stuck? Was a step unclear? Was a piece of information missing? Use their feedback to refine your documentation until it is completely foolproof.
Performing this drill once a year ensures your plan stays current and that your trusted parties are prepared. It transforms your crypto seed phrase storage from a static defense into a living, validated security system.
Got Questions About Seed Phrase Storage?
When you're dealing with Bitcoin every day, especially as a merchant, the little details of seed phrase security can feel overwhelming. Let's tackle some of the most common questions I hear, breaking them down with clear, practical advice rooted in real-world security.
Should I Add a BIP39 Passphrase?
Yes. Absolutely. Think of a BIP39 passphrase (sometimes called the "25th word") as a powerful second-factor for your physical backup. It’s an extra password that you never write down with your 12 or 24 words.
If a thief manages to get their hands on your metal seed plate, they’re still stuck. Without that passphrase, the words are useless. But this security comes with a heavy dose of personal responsibility: if you forget the passphrase, your funds are gone forever. You either commit it to memory—and I mean really commit it—or you store it somewhere completely separate and just as secure as your main seed phrase backup.
How Often Should I Check on My Backups?
You can't just set it and forget it. A quick physical inspection of your backups at least once per year is a non-negotiable part of good custody.
- Paper backups? Look for any fading, ink bleed, or water damage. Paper is incredibly fragile, and a yearly check can catch problems before your words become unreadable.
- Metal backups? You're checking for corrosion, physical damage, or any signs of tampering.
This annual check-in does more than just verify the physical state of your backup. It forces you to recall your storage locations and review your recovery plan, turning a passive security measure into an active, well-rehearsed process.
What's the Single Biggest Mistake Merchants Make?
Without a doubt, the most catastrophic mistake is any form of digital exposure. I'm talking about snapping a quick photo of the words, typing them into a notes app, saving them in a password manager, or even stashing them in an email draft.
Any device that has ever touched the internet is a potential liability. Once your seed phrase is in a digital environment, you have to assume it's compromised. The entire foundation of secure seed phrase management rests on maintaining a strict, end-to-end offline procedure, from generation all the way through to storage.
Is a Bank Safe Deposit Box a Good Idea?
A safe deposit box can be a fantastic piece of a larger security puzzle, but it should never be the whole puzzle. It offers professional-grade protection against common threats like theft or fire, which makes it a solid choice for one of your backups.
The danger is relying on it exclusively. That creates a single point of failure. Your access is limited by bank hours, holidays, and could even be restricted by legal orders. The smart play is to use a safe deposit box to store one of several backups, especially in a multisig setup where immediate access to any single key isn't critical. This way, you get the benefit of its high physical security without being hamstrung by its limitations.
Ready to accept Bitcoin payments directly and securely? Flash provides the tools for merchants to integrate wallet-to-wallet transactions instantly, with no intermediaries and minimal fees. Start accepting Bitcoin in under a minute and connect with a global user base. Learn more at the official Flash website.